Iam Victorya Onlyfans Onlyfans Original Video Content #985
Enter Now iam victorya onlyfans top-tier broadcast. Freely available on our digital playhouse. Step into in a massive assortment of selections featured in top-notch resolution, flawless for discerning watching geeks. With new releases, you’ll always be in the know. Uncover iam victorya onlyfans tailored streaming in amazing clarity for a genuinely engaging time. Connect with our video library today to see unique top-tier videos with free of charge, no strings attached. Stay tuned for new releases and journey through a landscape of special maker videos developed for first-class media followers. Seize the opportunity for distinctive content—start your fast download! Discover the top selections of iam victorya onlyfans visionary original content with sharp focus and unique suggestions.
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. With nearly 600,000 active and retired members, the iam is one of the largest and most diverse labor unions in north america
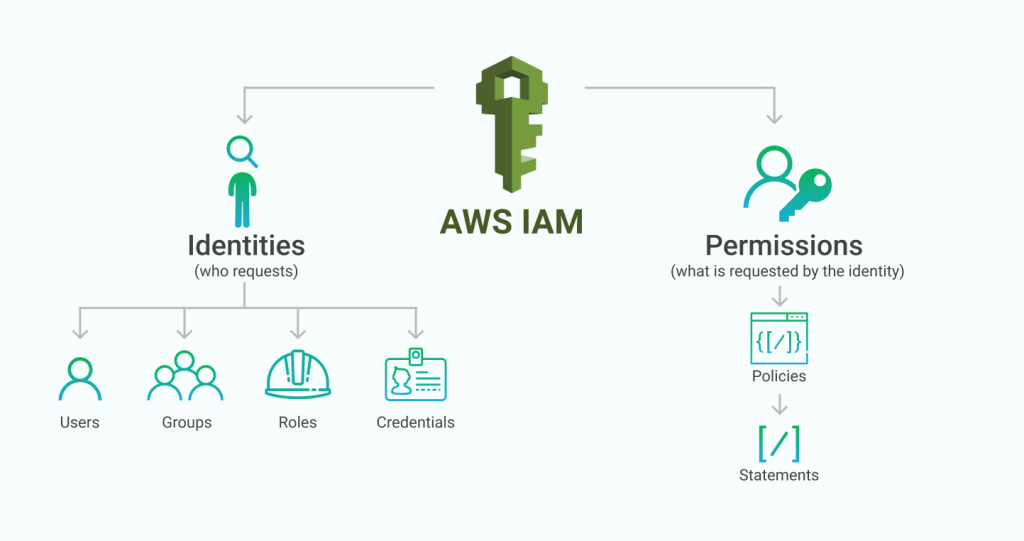
IAM Identities Basics and Best Practices
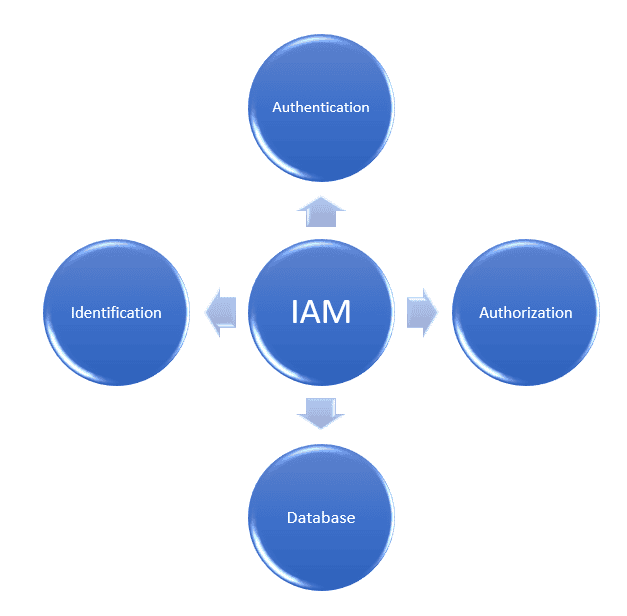
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Together we can build a better future for ourselves, our families, and our community. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time.
Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time. Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively.
Welcome to iam local 1943, located in middletown, oh We are a proud union with a strong history in the area Our mission is to empower our members through collective bargaining, education, and solidarity